Showing 1 - 12 of 31

DAR Series Part 1: Data Threats and Protection
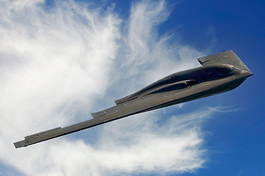
Classified data-at-rest (DAR) faces both internal and external threats that can subject sensitive data to exploitation. DAR is particularly at risk during missions if the deployed vehicle is lost but is also at risk during transport to and from the vehicle.
01/04/2024