
What is CSfC?
Commercial Solutions for Classified (CSfC) is an integral part of the National Security Agency (NSA)’s strategy to deliver secure cybersecurity solutions. The program leverages commercial encryption technologies, such as those employed in cars, mobile phones, tablets, and home security systems, to deliver cybersecurity solutions for classified applications quickly.
How CSfC Prescribes a Layered Approach to Data at Rest Encryption
Data at rest (DAR) can be threatened from four different vectors, some internal and some external. In deployed DAR applications (e.g., planes, helicopters, unmanned underwater vehicles, ground vehicles), vehicles may be lost during a mission. The data at rest can also be lost during transport from the deployed vehicle back and forth to the ground station. Once mission data has been safely downloaded and stored on a network, it is still at risk to relentless hackers (nation-state and independent) and unknown internal bad actors with malicious agendas.
CSfC is founded on the principle that properly configured, layered solutions can provide adequate protection of classified data in various applications. Two layers of data at rest encryption are required to be fielded as a solution.
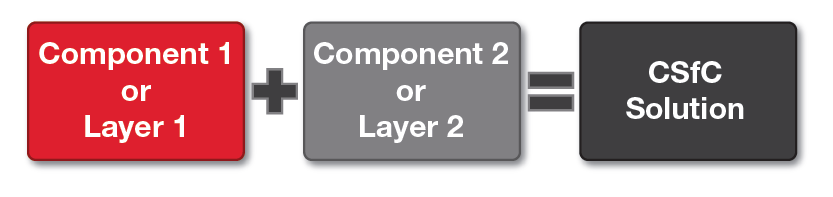
Figure 1 A CSfC solution requires two layers of DAR encryption
When properly implemented, a single layer of data at rest encryption fro