The National Institute of Standards and Technology (NIST) Federal Information Processing Standard FIPS 140-2 for Cryptography is an internationally recognized security certification standard for commercial cryptography. Applicable to both hardware and software based cryptography, the FIPS 140-2 standard sets out the requirements related to design, implementation, validation, and robustness to ensure cryptography equipment operates as expected.
Solutions designed to the FIPS 140-2 standard
Setting requirements for design, implementation, validation, and robustness in cryptography equipment
Cryptography refers to the algorithms and protocols used to secure or “hide” data from unauthorized access through encrypting and decrypting data. Common cryptography techniques include symmetric-key algorithms such as DES/3DES and AES and public-key algorithms such as RSA. Cryptography key management is also a significant factor in the FIPS 140-2 standard.
Modern cryptography is used today in almost all forms of commerce, such as the financial markets, internet data security, and the defense industry for data and communications security.
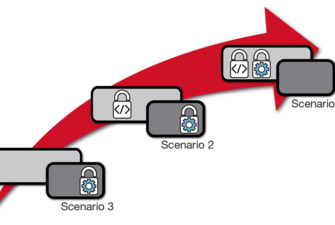
The FIPS 140-2 standard provides four increasingly higher levels of security, numbered Level 1 thru Level 4, covering a wide range of security applications and environments. Level 1 covers basic security, whereas Level 4 provides the highest level of security. Commercial FIPS 140-2 validated products are most commonly validated to Levels 2 or 3.
Equipment is evaluated independently, and validation is governed by the Cryptographic Module Validation Program (CMVP), a joint venture between the NIST in the United States and Canada's Communications Security Establishment (CSE).
Certification Authorities for Trusted Computing in Military & Avionics
This white paper provides an overview of some of the certification authorities that are involved in Trusted Computing, explores which disciplines they oversee, and gives guidance on when to get these certification authorities involved. While this white paper will focus specifically on the US market, it also discusses ways in which these bodies are relevant (or not) in some international markets.
Choosing the Best Location for Your Data-At-Rest Encryption Technology
This paper discusses the different places the encryption technology can be located on a data storage solution and aims to help you chose a solution that is best for your application.